What is a Security Assessment & Why it Matters for Associations

Taking a security assessment is the first step to getting ahead of cyber threats and developing a security culture. It gives you the lay of the land on your current performance across nine core IT security functions and prioritizes quick wins.
Luckily, an IT security assessment doesn’t take much work or time. But it’s vital to mold your cybersecurity posture and the road forward.
What is a security assessment?
An IT security assessment cuts through the noise and gives you the data you need to start your security management journey.
These survey-based or interview-based assessments measure the performance of core IT security areas. The goal is to pinpoint your most pressing vulnerabilities so you can prioritize rapid improvement.
Conducting a formal cyber assessment once a year is widely recommended to minimize your exposure to the growing threat landscape. A yearly evaluation allows you to proactively manage your risk by checking off action items on the priority list.
Why regular security assessments are a must for associations
A formal security assessment is necessary to strengthen your governance policies and procedures. With the expanding digital ecosystem and increasing sophistication of cyberattacks, doing a formal security assessment once a year is standard practice.
Data privacy and security have become a strategic value for mission-critical organizations, not just a compliance checklist. Crippling cyberattacks are escalating at an alarming rate year after year, causing larger and more frequent business interruptions.
Just look at the numbers:
- "Business interrupted" cyberattacks have increased 50% year over year.
- Cyber perils are the biggest concern for organizations globally in 2022.
- In 2020, 94% of organizations reported at least one "business interrupted" attack in 12 months.
- The volume and impact of breaches are disproportionately larger for smaller organizations.
Time and time again, common culprits that widen your exposure are a lack of security controls, delayed software updates (aka technical debt), and neglecting routine diagnostics. These risk factors indicate a weak security posture.
Only conducting a cyber assessment after a breach or just doing informal checks isn't gonna cut it either. These are glaring cyber vulnerabilities that make your systems easier to infiltrate and put your data at risk.
Point is, routine security assessments should be a priority for your association. Failing to prevent and minimize the impact of cyber-related events puts your organization on a collision course that can upend your short-term continuity and long-term organizational resilience.
What’s the purpose of formal security assessment?
An annual formal assessment helps your IT team and organization as a whole become proactive in your IT security governance and management. It allows you to achieve confidence and adaptability in security practices, gain buy-in from organizational leaders, and focus efforts on rapid improvement.
The three main goals include:
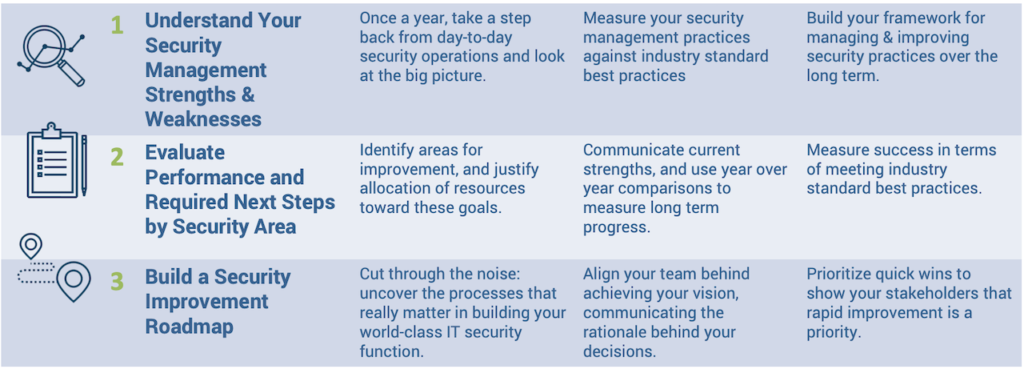
- Understand the strengths and weaknesses of your cybersecurity governance and management practices.
- Take a step back from the daily grind to see the big picture each year.
- Measure your cyber practices against current security best practices and industry standards.
- Build a long-term framework for managing and improving cybersecurity.
- Evaluate performance by security and next steps.
- Uncover areas for improvement and justify spending and resources toward these goals.
- Communicate strengths and measure year-over-year progress.
- Measure success in terms of meeting industry-standard best practices.
- Build an improvement roadmap.
- Prioritize quick wins and security processes that really matter for your organization.
- Align your IT team behind achieving the vision and communicate the rationale behind the importance of integrating information security governance into your IT strategy.
Discover quick wins across 9 key areas
Because measuring and communicating success in IT Security can be difficult, an overall benchmark score represents a summary indicator of where you're at in relation to industry standard best practices.
You ultimately get a Security Management Scorecard as well as improvement priorities across seven key IT security areas. A truly comprehensive assessment include the following IT functions:
Risk analysis - A review of risks (threats, likelihood, and impact) to information and/or systems, with the aim of minimizing risk to an acceptable level.
Compliance management - The process of ensuring the compliance objectives (regulatory, policy, or other) are being met.
Vulnerability management - The process of managing system vulnerabilities to reduce exposure to threats.
Auditing - The process of reviewing controls, along with supporting evidence, to ensure that policies and procedures are being followed.
Event and incident management - The process of managing potential and actual information security incidents and events that provide insight into such incidents.
Security culture - The overall stance of an organization, in terms of people and processes, related to the security of information and systems.
Policy and process governance - The management process to ensure your policies and processes are formalized, documented, enforced, and reviewed.
- Servers
- Apps
- Network
- Data
- Physical
- End User Devices
- Individual Access Management
Security training and assessment is the most effective way to mitigate this risk. Yet only 33% of IT staff regularly receive security training. A lack of security awareness training often leads to dramatic consequences simply because your people are often lax about cybersecurity requirements.
Without training, associations with remote workers will continue to be a target for cybercriminals. So will professional organizations and non-profits that put on online events and educational programs in which registrants have to log in to your server remotely.
This assessment tells you how to enhance security awareness training for end-users to deliver the most success with the least amount of effort. There are four core elements: methods, scope, frequency, and foundation.
The knowledge and diligence of IT staff are also evaluated as part of creating a culture of security and data privacy. To understand and perfect your organization’s level of “IT responsibility,” security assessments measure four core areas of include: expertise, assessment, end-user evaluation, and knowledge transfer.
How does it work?
The annual security assessment can be conducted as a group interview or via individual survey distribution. The same industry-standard survey questions are used.
At Cimatri, we prefer to run our security assessments as a group interview to get a full understanding of your organizational dynamics and security posture. The security assessment takes about 90 minutes (about 1 and a half hours) of your time.
There are three main phases:
- Participate in a structured group interview. This group interview is conducted with the head of IT and other leaders involved in security. Other participants may include your Chief Financial Officer (CFO), Chief Operating Officer (COO), and head of HR.
Read More: 14 Skills of Successful Association IT Leaders
- The data is analyzed and benchmarked. We send the data securely to our partners at InfoTech Research Group so it can be compared against industry standards and current cybersecurity best practices.
- You receive a report and verbal presentation. The final step is a comprehensive report of the IT Diagnostic Program, including your Security Management Scorecard and recommended actions and priorities. The documented results are supplemented by a verbal presentation.
Who is it for?
For formal cybersecurity assessments conducted through an outside expert like Cimatri, the intended audience includes IT security leaders as well as other organizational leaders (e.g. CFO, COO, and HR lead).
Read More: Do I need CIO services?
Your IT leaders oversee your information security so, naturally, they should complete the assessment for your organization. They should also be the ones in charge of directing improvement efforts and closing the gaps in your security governance and management.
How do you perform a security assessment?
Here are the main steps and processes involved in a cyber diagnostic. This is essentially what we deliver and present to our clients in their security governance and management report.
- Evaluate overall security maturity across 7 governance areas. Determine which areas require the most improvement and investigate improvement opportunities.
- Assess process maturity across 7 areas of security. Determine which areas require the most improvement and investigate process improvement opportunities.
- Get a prioritized list of security areas requiring immediate attention. This list is used to focus work effort and build improvements.
- Evaluate the effectiveness of individual security governance areas. For low-scoring areas, follow recommended actions to start improvement efforts.
- Get a list of recommendations for improvement. Start checking off the action items and perfecting policies and processes as needed.
- Access process maturity of individual security areas. Determine which processes are missing or have not been formalized.
- See which processes are lacking clear accountability. Assign accountability against key processes.
What are the benefits?
Systematic governance is the best insurance against rapidly evolving security threats and multi-stage attacks. Documenting your IT security policies and procedures reinforces data governance, ownership, and organization-wide cyberculture.
You're able to make better, faster decisions and more quickly respond to theft, intrusions, and breaches. When systematic governance falls through, cyber risk insurance is your association’s last line of defense against cyberattacks and the damage caused to your reputation, finances, and strategic priorities. Formal security assessments should cover this insurance with you.
Not only does this help you avert cybercriminals and their increasingly sophisticated and unpredictable attacks, but formal security governance practices and a strong data privacy culture support your digital transformation journey. It allows you to break down digital silos and stimulate ongoing collaboration and coordination between stakeholders at all levels.
When you're practicing regular security hygiene including patching, network segmentation, and employee education, you're able to innovate safely and minimize the risks associated with continuous process improvement.
As you begin your map out and create new value streams, you’ll be able to communicate the value of cybersecurity leadership and management in protecting these assets and process efficiencies. Formal governance practices even serve to clarify your organizational goals and security protocols when aligned to your IT and organizational strategy.
Read More: ROI of Business-Aligned Security for Associations
Getting Started
Take the first step to effectively managing your IT security. Learn more about our Security Assessment for Associations.